SECURITY SOLUTIONS
Integrated Security
Solutions That Work Together, Not in Silos
Modern threats require a connected defense. We unify your security tools, systems, and processes to eliminate gaps, reduce complexity, and deliver real-time protection across your entire environment.
Trusted by security-first enterprises, SaaS platforms, and regulated industries
Most companies use disconnected tools.
No visibility
Delayed response
Security gaps

OUR CORE SERVICES
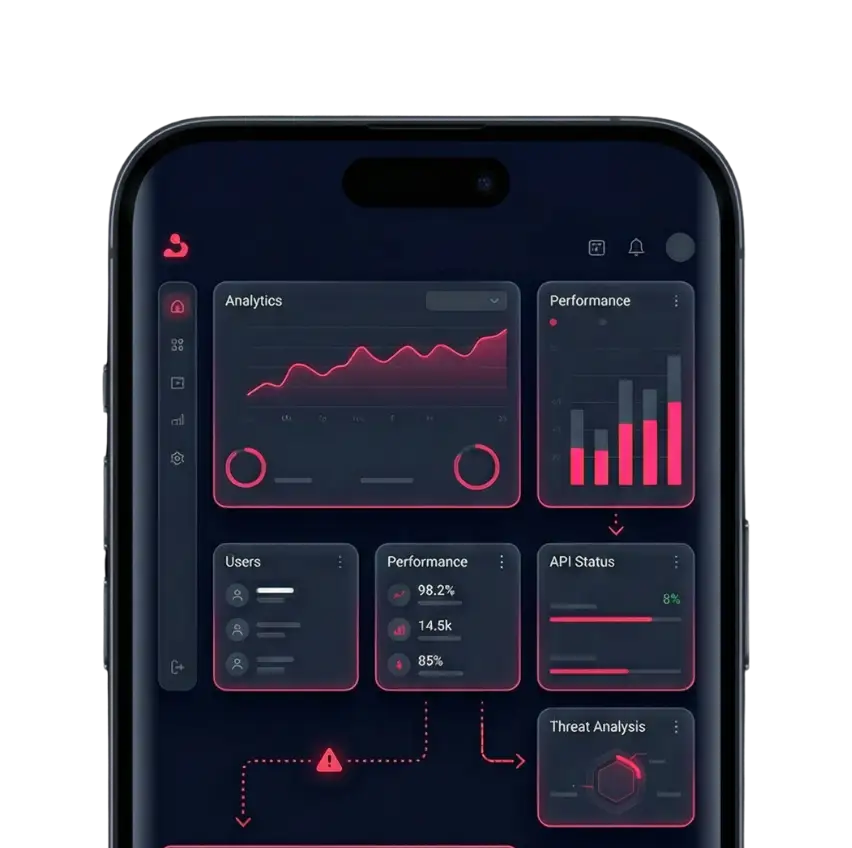
Unified Security
Across Your Entire Environment
We integrate your security tools, data, and workflows into a single, cohesive system that eliminates blind spots, improves visibility, and enables faster, more effective threat response.
- Identity and Access Management
- Data Loss Protection
- SIEM
- Cloud Security
- AI Security
- Threat Intelligence Platforms
Identity and Access Management
Ensure only the right users access critical systems at the right time.
- Enforce least privilege
- Implement MFA
- Secure identities
- Reduce access risks

Data Loss Protection
Prevent sensitive data from being exposed or misused.
- Monitor data movement
- Prevent leaks
- Protect critical data
- Enforce policies

SIEM
Centralize your security data for real-time threat detection.
- Detect anomalies
- Enable fast response
- Improve visibility
- Strengthen monitoring

Cloud Security
Ensure consistent protection across cloud environments.
- Monitor activity
- Detect threats
- Maintain compliance
- Automate response

AI Security
Protect AI systems from manipulation and misuse.
- Secure models
- Prevent leakage
- Protect workflows
- Ensure trust

Threat Intelligence Platforms
Stay ahead of evolving cyber threats with actionable intelligence.
- Identify threats early
- Strengthen defense
- Improve readiness
- Enable proactive response

OUR CORE SERVICES
Unified Security
Across Your Entire Environment
We integrate your security tools, data, and workflows into a single, cohesive system that eliminates blind spots, improves visibility, and enables faster, more effective threat response.
- Identity and Access Management
- Data Loss Protection
- SIEM
- Cloud Security
- AI Security
- Threat Intelligence Platforms
Identity and Access Management
Ensure only the right users access critical systems at the right time.
- Enforce least privilege
- Implement MFA
- Secure identities
- Reduce access risks
Data Loss Protection
Prevent sensitive data from being exposed or misused.
- Monitor data movement
- Prevent leaks
- Protect critical data
- Enforce policies
SIEM
Centralize your security data for real-time threat detection.
- Detect anomalies
- Enable fast response
- Improve visibility
- Strengthen monitoring
Cloud Security
Ensure consistent protection across cloud environments.
- Monitor activity
- Detect threats
- Maintain compliance
- Automate response
AI Security
Protect AI systems from manipulation and misuse.
- Secure models
- Prevent leakage
- Protect workflows
- Ensure trust
Threat Intelligence Platforms
Stay ahead of evolving cyber threats with actionable intelligence.
- Identify threats early
- Strengthen defense
- Improve readiness
- Enable proactive response
HOW WE HELP
How We Secure AI Systems
A structured, end-to-end approach to protect AI pipelines, prevent exploitation, and ensure secure deployment at scale.
01
Threat Modeling
Identify risks across your AI pipelines before attackers exploit them. We map vulnerabilities, attack surfaces, and potential failure points early.
02
Secure Deployment
Design and implement secure architectures for AI models and systems. We ensure safe deployment across cloud, APIs, and production environments.
03
Adversarial Testing
Simulate real-world attacks to uncover hidden weaknesses. Our red teaming approach tests how your AI behaves under adversarial conditions.
04
Data Protection
Prevent data leakage and ensure privacy across AI workflows. We secure sensitive inputs, outputs, and model interactions from exposure.
WHY CANUM AI
THE PRINCIPLES THAT DRIVE US
🧠
Faster Response
Detect and respond to threats in real time, reducing dwell time and minimizing potential damage.
⚡
Better Visibility
Gain complete insight across your systems, users, and data to identify risks before they escalate.
🏢
Reduced Complexity
Streamline your security stack by integrating tools and processes into a unified, manageable system.
🔥
Stronger Defense
Build layered protection that adapts to evolving threats and safeguards your entire environment.
Stop managing tools. Start managing security
GET IN TOUCH
// SECURE CHANNEL ENCRYPTED SUBMISSION