CLOUD & INFRA SECURITY
Your Infrastructure Is
Your Backbone. Make It Unbreakable
From misconfigurations to advanced threats, your infrastructure is constantly exposed. We secure cloud environments, networks, and systems to prevent breaches, ensure resilience, and keep your operations running without disruption.
Trusted by security-first enterprises, SaaS platforms, and regulated industries
Cloud environments are complex and often misconfigured.
Exposed storage
Weak IAM controls
Poor network segmentation
Most breaches today happen due to misconfiguration.


OUR CORE SERVICES
Comprehensive Protection for
Modern Infrastructure
We combine cloud security, network protection, and continuous monitoring to ensure your infrastructure remains resilient, compliant, and secure at scale.
Cloud Security
Secure your cloud infrastructure by identifying misconfigurations and access risks. We align your environment with industry best practices and zero trust principles.
- Identify and fix misconfigurations
- Strengthen access control
- Secure storage and services
- Align with best practices

Data Center Security
Protect your infrastructure with layered controls across physical and virtual systems.
- Secure infrastructure access
- Monitor system activity
- Prevent unauthorized access
- Strengthen resilience

Network Security
Design networks that limit attacker movement and contain threats effectively.
- Implement segmentation
- Prevent lateral movement
- Monitor traffic patterns
- Strengthen defenses

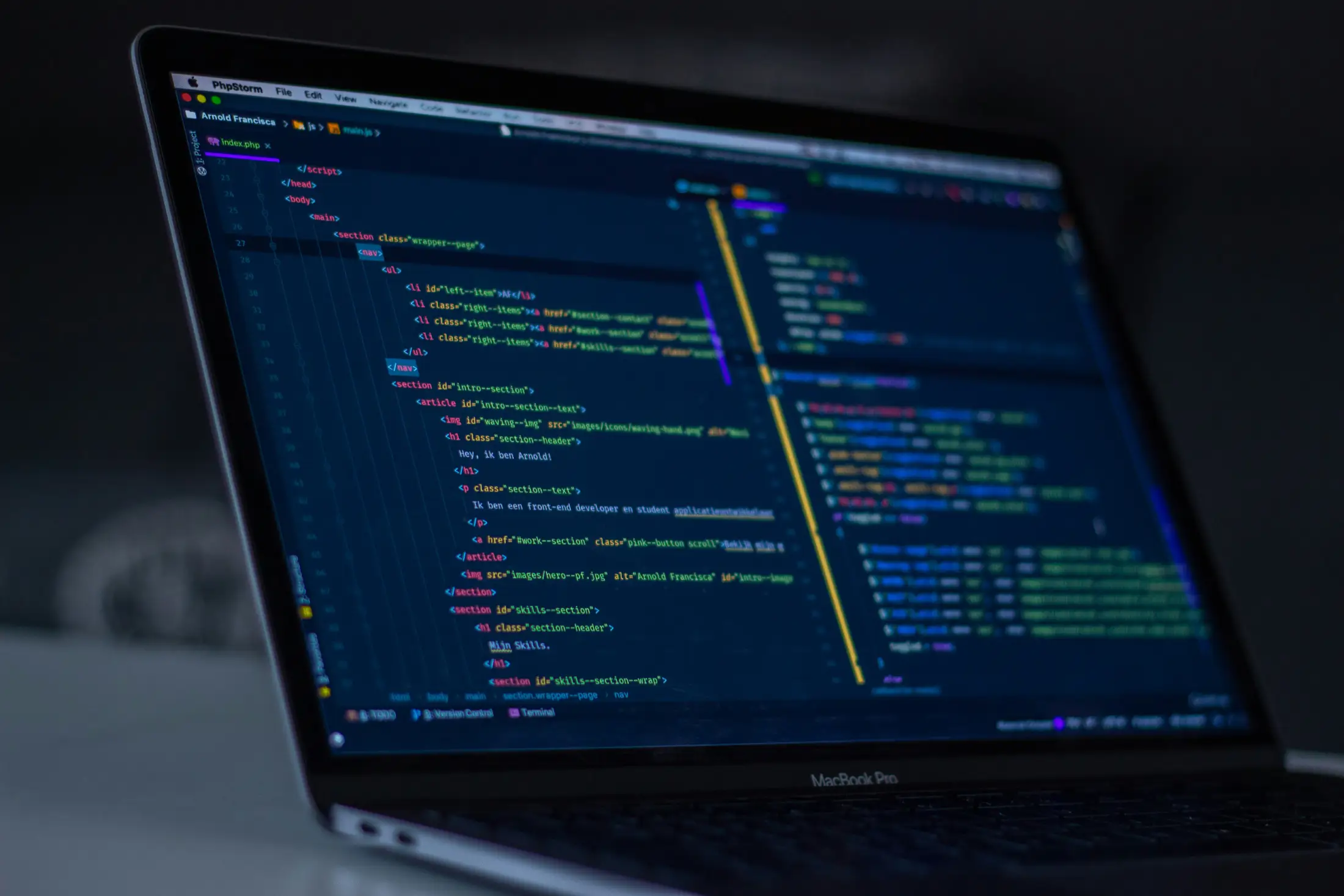
OS Security
Harden operating systems to eliminate vulnerabilities and reduce attack surface.
- Apply secure configurations
- Patch vulnerabilities
- Reduce exposure
- Strengthen endpoints

WHAT WE IMPLEMENT
How We Secure
Cloud & Infrastructure
We implement security across your cloud and infrastructure by eliminating misconfigurations, strengthening access controls, and ensuring continuous visibility into risks.
01
Cloud Posture
Identify and fix misconfigurations across your cloud environments. We ensure your infrastructure follows security best practices and remains compliant at scale.
02
IAM Control
Strengthen identity and access management across systems. We optimize permissions, enforce least privilege, and prevent unauthorized access.
03
Network Design
Build secure and resilient network architectures. We segment environments, secure traffic flows, and reduce exposure to external threats.
04
Monitoring
Maintain continuous visibility across your infrastructure. We detect anomalies, respond to threats, and ensure ongoing protection in real time.
WHY CANUM AI
THE PRINCIPLES THAT DRIVE US
🧠
Reduced Breach Risk
Minimize vulnerabilities and eliminate attack entry points before they can be exploited by threat actors.
⚡
Stronger Security Posture
Build a resilient infrastructure with layered defenses that adapt to evolving threats and protect critical assets.
🏢
Compliance Readiness
Align your systems with industry standards and regulatory requirements to avoid penalties and ensure audit success.
🔥
Operational Stability
Maintain uninterrupted performance with secure, well-configured systems that reduce downtime and prevent disruptions.
Build a secure foundation for your digital operations
GET IN TOUCH
// SECURE CHANNEL ENCRYPTED SUBMISSION