APPLICATION SECURITY
Your Applications Are the
Front Door. Secure Them Before Attackers Walk In
Your applications are the first target for attackers. We identify vulnerabilities, simulate real-world attacks, and secure every entry point before they can be exploited.
Trusted by security-first enterprises, SaaS platforms, and regulated industries
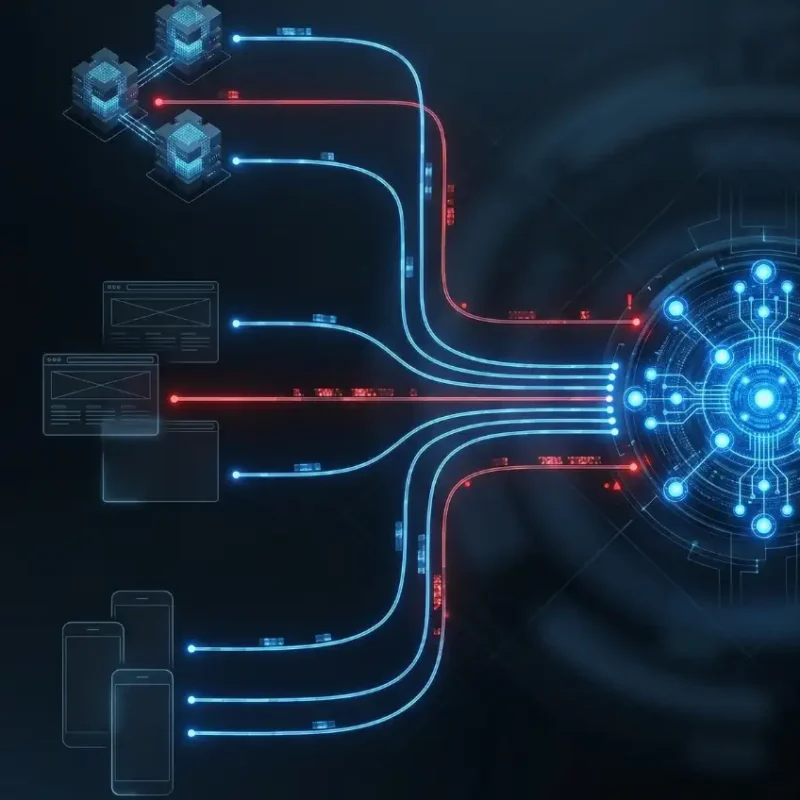
Every API, web app, and mobile app is a potential entry point.
APIs expose sensitive logic
Web apps are vulnerable to attacks.
Mobile apps leak data and keys
Attackers don’t break in. They log in through your vulnerabilities.
OUR CORE SERVICES
Comprehensive Security for
Every Layer of Your Applications
From code to deployment, we identify vulnerabilities, simulate real-world attacks, and secure your applications against evolving threats before they can be exploited.
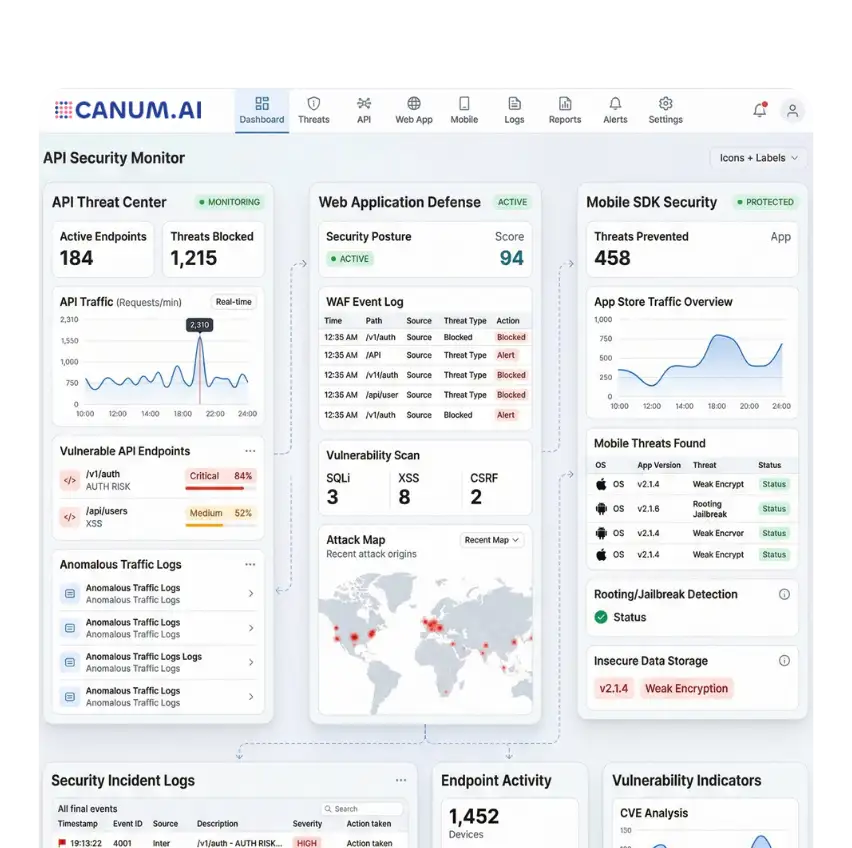
API Security
Secure your APIs against unauthorized access, data exposure, and abuse. We analyze authentication flows, rate limits, and endpoint vulnerabilities to ensure your APIs cannot be exploited.
- Prevent unauthorized API access and abuse
- Secure authentication and token flows
- Protect sensitive data in transit
- Identify hidden endpoint vulnerabilities

Application Security
Modern applications are complex and constantly evolving. We help you detect and fix vulnerabilities before they impact your business.
- Identify business logic and code-level flaws.
- Perform deep vulnerability assessments
- Strengthen application architecture
- Reduce risk before production release

Web App Security
Continuous attacks target web applications. We simulate real-world threat scenarios to uncover vulnerabilities and strengthen your defenses.
- Protect against OWASP risks
- Detect injection and authentication flaws
- Prevent session hijacking
- Improve application resilience

Mobile App Security
Mobile apps often expose critical business logic and data. We ensure your app is secure across environments.
- Prevent reverse engineering
- Secure local storage
- Protect API integrations
- Identify platform-specific risks

HOW WE HELP
How We Protect
Applications in Real Environments
From identifying vulnerabilities to securing code and monitoring live systems, we implement security across every stage of your application lifecycle.
01
VAPT Testing
Identify and exploit vulnerabilities before attackers do. We simulate real-world attack scenarios to uncover critical security gaps.
02
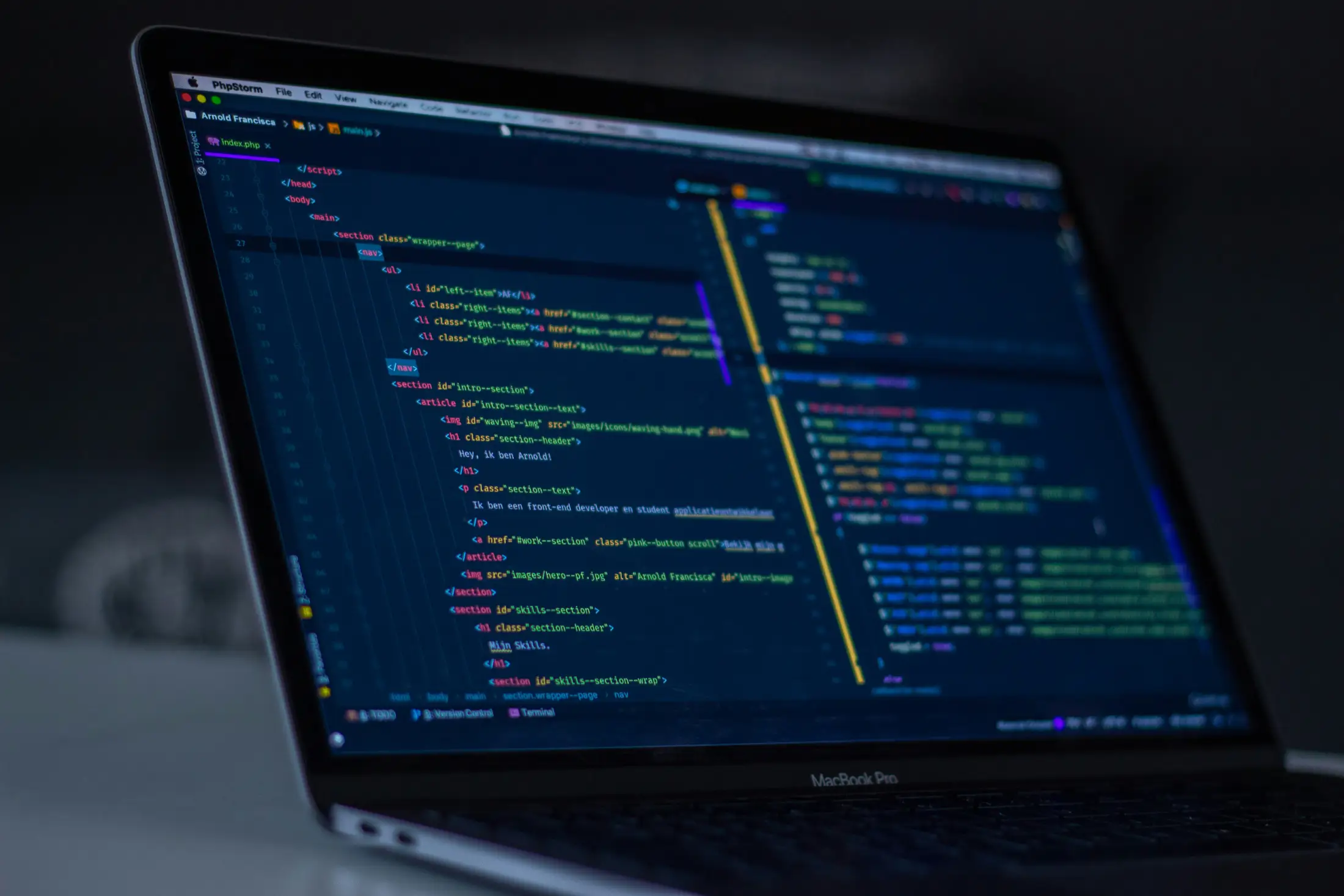
Code Review
Detect security flaws at the code level early. We analyze logic, dependencies, and configurations to eliminate hidden risks.
03
DevSecOps
Integrate security into your development pipeline. We ensure continuous security across builds, deployments, and updates.
04
Runtime Protection
Secure applications in live environments. We monitor, detect, and respond to threats in real time.
WHY CANUM AI
THE PRINCIPLES THAT DRIVE US
🔒
Data Breaches
Sensitive data exposure can disrupt operations, trigger legal action, and lead to long-term security risks if not contained early.
💸
Revenue Loss
Security incidents cause downtime, disrupted services, and unexpected costs that directly impact your bottom line.
🤝
Customer Trust Damage
A single breach can erode years of trust, making it difficult to retain customers and maintain your brand reputation
⚖️
Compliance Penalties
Failure to meet regulatory standards can result in heavy fines, legal consequences, and operational restrictions.
Secure your applications before attackers find the gap.
GET IN TOUCH
// SECURE CHANNEL ENCRYPTED SUBMISSION